Nexus Platform
Where Security Operations Converge
Nexus GRC
Complete governance, risk, and compliance management with automated workflows and real-time reporting.
- Risk Management
- Policy Management
- Compliance Tracking
- Audit Management
Nexus SOC Case Mgmt
Security operations case management with threat detection, incident response, and team coordination.
- Threat Detection & Analysis
- SOC Team Management
- Incident Workflow
- Case Tracking
Nexus IR
Comprehensive incident management with playbooks, tabletop exercises, and real-time tracking.
- IR Playbooks
- Incident Tracking
- Tabletop Exercises
- Timeline Management
Nexus Pentest
Advanced penetration testing tools with automated scanning and detailed reporting.
- Automated Scanning
- Manual Testing Tools
- Remediation Tracking
- Compliance Reports
Vulnerability Mgmt
Centralized vulnerability management with scanner integration and risk-based prioritization.
- Tenable/Nessus Import
- Risk Prioritization
- Asset Correlation
- Remediation Workflows
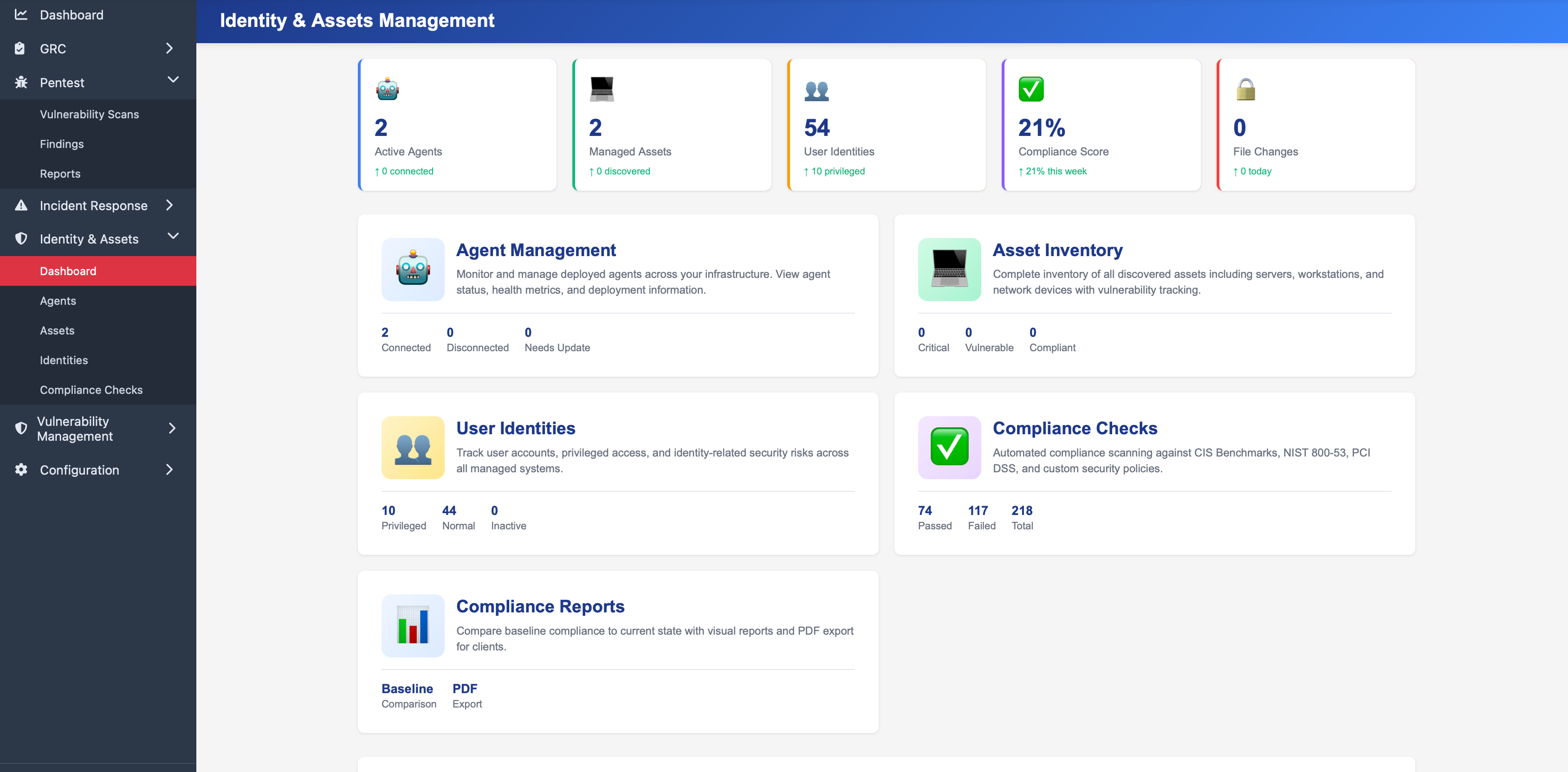
Identity & Compliance
Agent-based compliance monitoring with identity analysis and baseline security testing.
- Agent-Based Compliance
- Baseline Testing
- Identity Analysis
- CIS Benchmarks
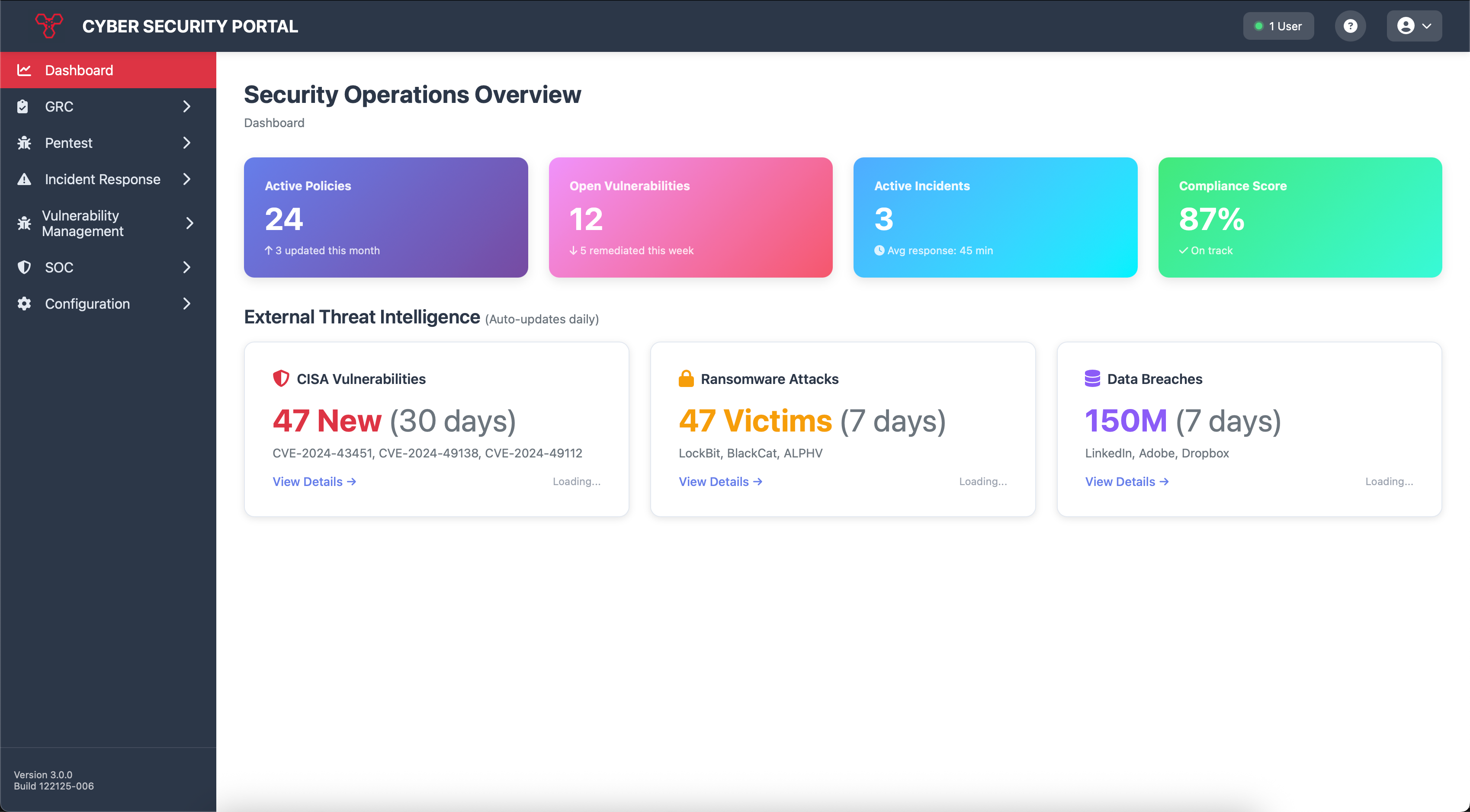
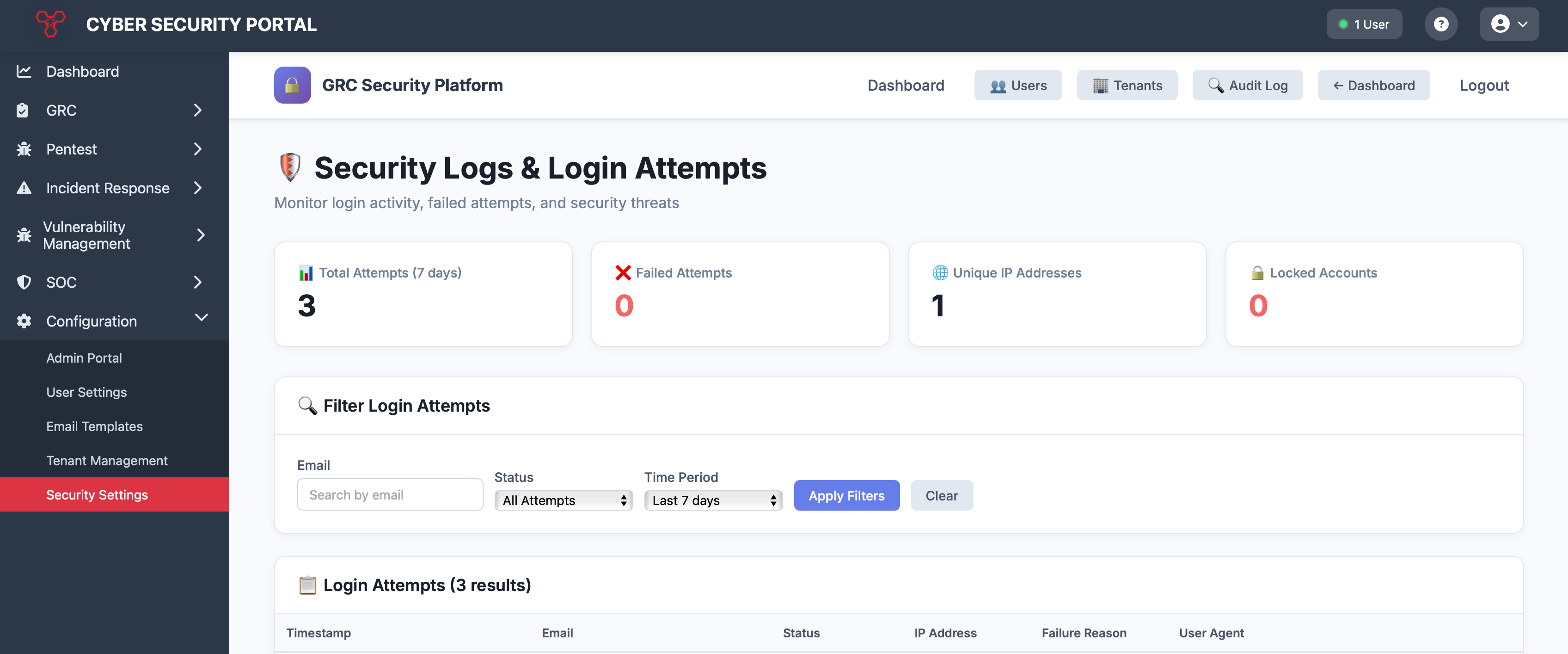
Platform Screenshots
Professional Services
Expert consulting and managed services to accelerate your security program
Our team of certified security professionals provides comprehensive consulting services to help organizations build, maintain, and optimize their security programs. From initial assessments to ongoing management, we deliver expert guidance tailored to your industry and regulatory requirements.
Risk Management Services
Comprehensive risk assessment and management programs designed to identify, evaluate, and mitigate organizational risks across all business functions.
What We Deliver:
- Enterprise Risk Assessments: Comprehensive evaluation of organizational risks including operational, financial, strategic, and compliance risks
- Risk Register Development: Creation and maintenance of centralized risk repositories with scoring, ownership, and mitigation tracking
- Risk Treatment Planning: Development of actionable risk mitigation strategies aligned with business objectives and risk appetite
- Third-Party Risk Management: Vendor risk assessment programs including due diligence, ongoing monitoring, and contract risk analysis
- Business Impact Analysis: Identification of critical business functions and assessment of potential impact from various risk scenarios
- Risk Reporting & Metrics: Executive dashboards and KRI development for board-level risk visibility
IT Gap Analysis
Detailed assessment of your current IT security posture against industry frameworks and best practices to identify gaps and prioritize remediation efforts.
What We Deliver:
- Framework Alignment Assessment: Comprehensive gap analysis against NIST CSF, ISO 27001, CIS Controls, SOC 2, and other relevant frameworks
- Technical Control Review: Evaluation of existing security controls including network security, access management, encryption, and monitoring capabilities
- Policy & Procedure Analysis: Assessment of documentation completeness, accuracy, and alignment with operational practices
- Compliance Readiness Review: Evaluation of preparedness for regulatory audits (HIPAA, PCI DSS, CMMC, FedRAMP, etc.)
- Maturity Assessment: Current-state analysis with maturity scoring and roadmap to target state
- Prioritized Remediation Plan: Risk-based prioritization of gaps with effort estimates, resource requirements, and implementation timelines
Vulnerability Management
Continuous vulnerability assessment and remediation program to identify, prioritize, and address security weaknesses before they can be exploited.
What We Deliver:
- Vulnerability Scanning Program: Deployment and management of automated scanning tools for network, application, and cloud infrastructure
- Penetration Testing: Manual security testing including external, internal, web application, and API penetration tests
- Vulnerability Prioritization: Risk-based scoring using CVSS, EPSS, and business context to focus remediation efforts
- Remediation Tracking: Workflow management for vulnerability remediation with SLA tracking and escalation procedures
- Patch Management Support: Assistance with patch testing, deployment planning, and emergency patching procedures
- Continuous Monitoring: Ongoing vulnerability assessment with trend analysis and executive reporting
- Threat Intelligence Integration: Correlation of vulnerabilities with active threat campaigns and exploit availability
Compliance Program Management
End-to-end compliance program development and management services to achieve and maintain certification across multiple regulatory frameworks.
What We Deliver:
- Compliance Roadmap Development: Strategic planning for achieving certifications (ISO 27001, SOC 2, HITRUST, FedRAMP, etc.)
- Policy & Procedure Development: Creation of comprehensive security policies, standards, and procedures aligned with framework requirements
- Control Implementation: Hands-on assistance implementing required security controls and evidence collection processes
- Audit Preparation: Pre-audit assessments, evidence gathering, and audit coordination services
- Continuous Compliance: Ongoing monitoring, control testing, and evidence management to maintain certification
- Multi-Framework Optimization: Unified control framework to satisfy multiple compliance requirements efficiently
Threat Pressure Services
Proactive threat assessment and security pressure testing to identify vulnerabilities before attackers do.
What We Deliver:
- External Threat Assessment: Comprehensive analysis of your external attack surface and exposure
- Penetration Testing: Simulated attacks to identify exploitable vulnerabilities in your infrastructure
- Red Team Exercises: Advanced adversary simulation to test detection and response capabilities
- Social Engineering Tests: Phishing, vishing, and physical security assessments
- Vulnerability Assessment: Systematic identification and prioritization of security weaknesses
- Attack Path Analysis: Mapping potential attack vectors and lateral movement opportunities
- Remediation Guidance: Actionable recommendations with prioritized remediation roadmap
Security Awareness Training
Comprehensive security awareness and training programs to build a security-conscious culture and reduce human-related security risks.
What We Deliver:
- Custom Training Programs: Role-based security training tailored to your organization's specific risks and industry
- Phishing Simulation: Realistic phishing campaigns with tracking, reporting, and targeted remediation training
- Security Champions Program: Development of internal security advocates across business units
- Executive Briefings: Board and C-level security awareness sessions focused on governance and risk
- Compliance Training: Specialized training for regulatory requirements (HIPAA, PCI DSS, etc.)
- Metrics & Reporting: Training effectiveness measurement and continuous improvement programs
Supported Compliance Frameworks
Simple, Transparent Pricing
Choose the plan that fits your organization
Nexus Essentials
- Nexus GRC
- Policy Management
- Compliance Module
- Up to 2 users
- 1 tenant
- Email support
Support Services
- Email support (48hr response)
- Technical support
- Security consulting
- Managed services
Nexus Professional
- Everything in Essentials
- Third Party Risk Management
- Vulnerability Management
- Up to 5 users
- 3 tenants
- Priority support
Support Services
- Priority support (24hr response)
- Technical support
- Security consulting (10hrs/mo)
- Managed services
Nexus Enterprise
- Everything in Professional
- Nexus IR
- Nexus Pentest
- Identity & Compliance Services
- Unlimited users & tenants
- Custom integrations
Support Services
- Dedicated support (4hr response)
- 24/7 technical support
- Security consulting (unlimited)
- Managed services available
Add-Ons
Why Cobalt Security?
Fast Implementation
Get up and running in days, not months. Our platform is designed for rapid deployment.
Multi-Tenant Ready
Perfect for MSPs and enterprises managing multiple organizations from one platform.
Scalable
Grows with your organization from startup to enterprise without missing a beat.
Secure by Design
Built with security-first architecture and industry best practices.
Ready to Get Started?
Contact us for a demo or to discuss your security needs